There is a lot of information on the web regarding Azure AD password reset, setup and related issues. In this Blog we want to focus on a few specific user password reset issues, which we have continuously seen over time. Internet articles and forums suggest various fixes for these, but often these solutions are confusing, not needed at all or not in depth enough. Administrator efforts to resolve these issues usually take way longer than expected. In this article we will assume we have a hybrid environment, which means Azure AD + domain controller (Azure hosted VM or on-prem). Let’s split the article into two sections – password reset via Azure portal and self-service password reset (SSPR).
Common issues when resetting user password via Azure portal
“Unfortunately, you cannot reset this user's password due to a policy or error in your on-premises environment” or
"Unfortunately, you cannot reset this user's password because your on-premises policy does not allow it. Please review your on-premises policy to ensure that it is setup correctly".
First, make sure new password meets GPO or local policies password requirements.
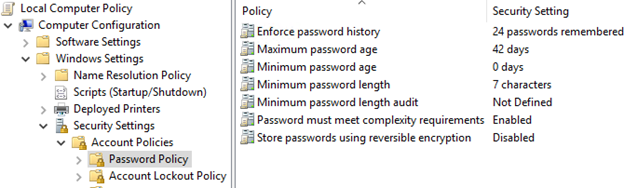
Firstly, pay attention to the “Minimum password age” attrubute.If it is not “0 days”, it means that it is not possible to reset the password twice that same day.
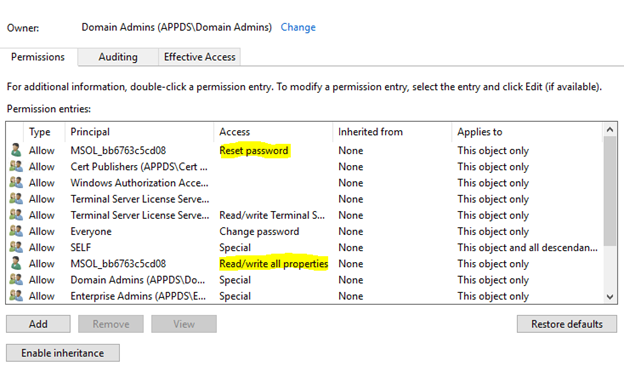
Secondly, check if the Azure AD Connect MSOL account (MSOL_************) has “Reset Password” permission on the specific user AD object, or inherits it from domain security properties. Not sure if all “Read/write all properties” are mandatory or could be more granular, but these are created as default, which does not apply to “Reset Password” permission unfortunately.
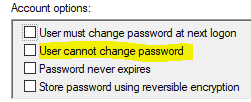
Thirdly, for obvious reasons – "User cannot change password" must be unchecked in the AD user account options.
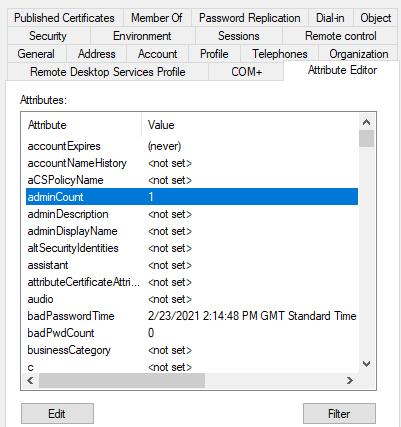
The fourth, and most tricky one; if the user account was ever added to Administrators, Account Operators or other protected groups ( https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/plan/security-best-practices/appendix-c--protected-accounts-and-groups-in-active-directory ), this will add “adminCount” attribute value as “1” on the user’s AD account object. For some reason, even removing the user account from any of the protected groups, the attribute may still stay at “1” and must be changed to “<not set>” or “0”. If not; password resets will not be allowed.
"We're sorry, we're not able to reset this user's password right now. This may be due to temporary issues on our end. Please wait a few minutes and try again".
As described in the error, this issue can be due to an issue on the Azure end, but more likely it is related to Azure AD connect 'health'. So, investigate that first and confirm that the “Microsoft Azure AD Sync” service is running all the time. Our advice is to add this service to monitoring for easier troubleshooting.
Self-service password reset (SSPR) in Azure Active Directory – things to know
For SSPR to work properly in the hybrid environment, the password on-prem writeback feature is mandatory. Required premium licensing and more details can be found in the below Microsoft article:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-sspr-licensing
We would like to add that Enterprise Mobility + Security E3 or A3 (E5 or A5), Microsoft 365 E3 or A3 (E5 or A5) and Microsoft 365 F1 will meet this prerequisite as well.
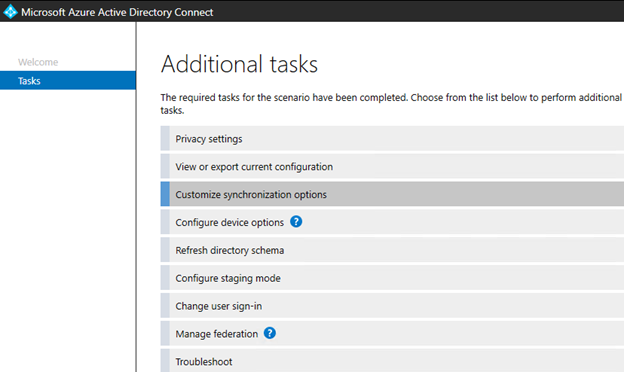
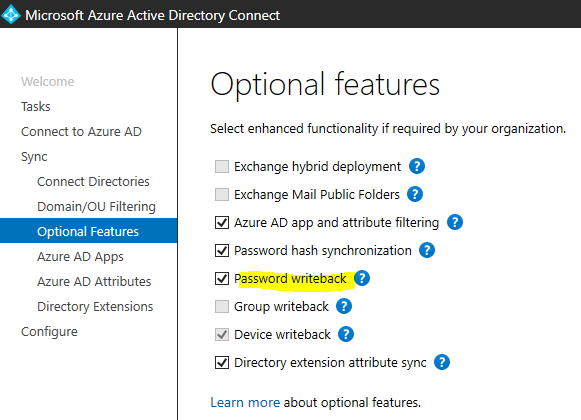
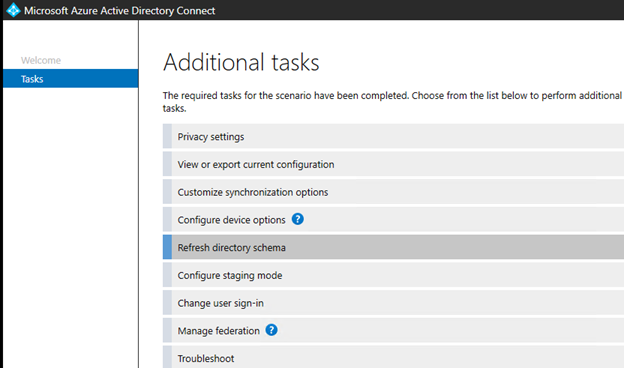
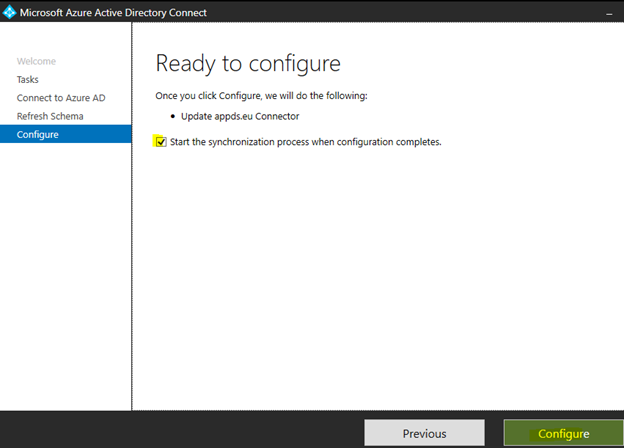
Password write back must be enabled in Azure AD Connect (installed on the domain controller) synchronization options and the steps, to do so, are shown in the following screenshots.
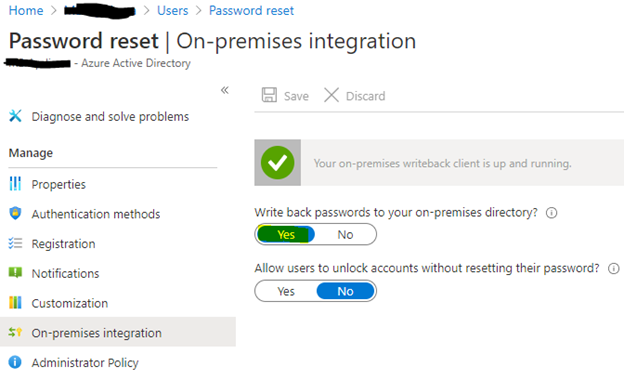
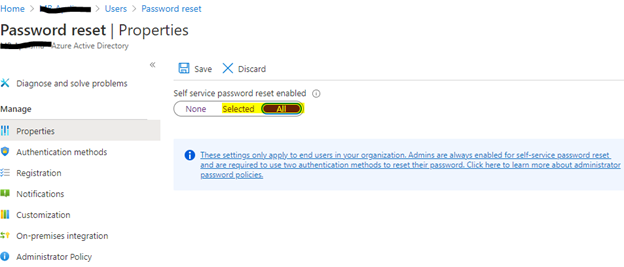
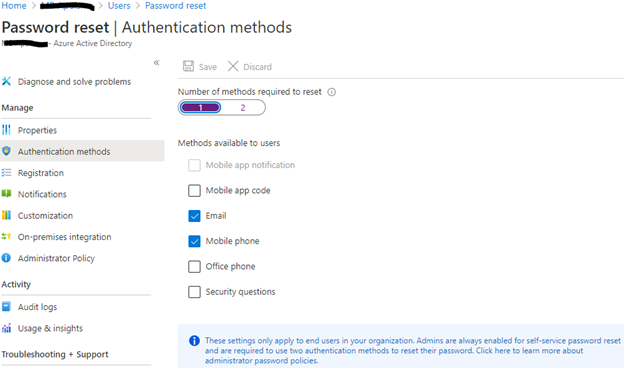
Do not miss to enable below two settings in the Azure Active Directory -> Users blade.
SSPR can be enabled for all users or selected AD groups. Possible error if not enabled yet: “SSPR_0011: Your organization hasn’t set up a password reset policy”.
Make sure that the Azure AD Connect MSOL account (MSOL_************) has “Reset Password” permission on the on-prem Active Directory user object, and run through the other useful tips/checks , to troubleshoot common issues, described in the beginning of this article. Possible error: “SSPR_0029: Your organization hasn’t properly set up the on-premises configuration for password reset”.
Complete the user SSPR registration activity if not done alreadydone. Registration process can be completed via https://aka.ms/ssprsetup. Authentication methods depending on the settings in Azure AD.
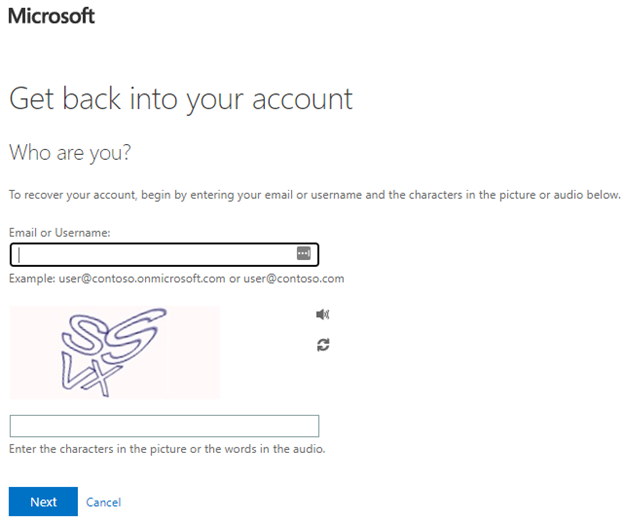
To finally self-reset the password, just go to https://passwordreset.microsoftonline.com/ and follow the steps.
In-depth SSPR guidelines can be found here - https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-sspr-deployment
In the final notes of the article, we would like to mention that due to the synchronization schedule between Azure AD and on-premise domain controller(s), there are times when data on both sides can be different. So when troubleshooting similar Active directory related issues, results may be misleading. It is extremely important to sync everything before the next test. This can be achieved by simply starting the Azure AD Connect tool, selecting “Refresh directory schema”, running through the wizard and checking the start the synchronization process tick box.

Hi, I want to subscribe for this webpage to get hottest updates, therefore where can i do it please help out. - Saturday, July 24, 2021
Hi, I want to subscribe for this webpage to get hottest updates, therefore where can i do it please help out.
I am in fact delighted to read this weblog posts which contains lots of useful data, thanks for providing these information. - Friday, July 9, 2021
I am in fact delighted to read this weblog posts which contains lots of useful data, thanks for providing these information.
Wow! After all I got a web site from where I know how to genuinely take useful facts regarding my study and knowledge. - Monday, July 5, 2021
Wow! After all I got a web site from where I know how to genuinely take useful facts regarding my study and knowledge.
Very soon this website will be famous amid all blogging people, due to it's pleasant posts - Sunday, July 4, 2021
Very soon this website will be famous amid all blogging people, due to it's pleasant posts
Hi there friends, nice piece of writing and good urging commented at this place, I am really enjoying by these. - Saturday, July 3, 2021
Hi there friends, nice piece of writing and good urging commented at this place, I am really enjoying by these.
I love it when individuals come together and share ideas. Great website, stick with it! - Thursday, July 1, 2021
I love it when individuals come together and share ideas. Great website, stick with it!
What's up, I read your new stuff regularly. Your story-telling style is awesome, keep up the good work! - Wednesday, June 30, 2021
What's up, I read your new stuff regularly. Your story-telling style is awesome, keep up the good work!
Excellent blog post. I definitely love this site. Keep it up! - Tuesday, June 29, 2021
Excellent blog post. I definitely love this site. Keep it up!
Way cool! Some extremely valid points! I appreciate you penning this write-up and the rest of the site is also very good. - Monday, June 28, 2021
Way cool! Some extremely valid points! I appreciate you penning this write-up and the rest of the site is also very good.
Excellent post. I am experiencing some of these issues as well.. - Saturday, June 26, 2021
Excellent post. I am experiencing some of these issues as well..
This is a topic which is near to my heart... Take care! Where are your contact details though? - Friday, June 25, 2021
This is a topic which is near to my heart... Take care! Where are your contact details though?
Incredible points. Great arguments. Keep up the great effort. - Thursday, June 24, 2021
Incredible points. Great arguments. Keep up the great effort.
Wonderful article! We are linking to this particularly great article on our site. Keep up the great writing. - Saturday, June 19, 2021
Wonderful article! We are linking to this particularly great article on our site. Keep up the great writing.